Low: 源代码:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 <?php if ( isset ( $_POST[ 'Upload' ] ) ) { $target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/" ; $target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] ); if ( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) { echo '<pre>Your image was not uploaded.</pre>' ; } else { echo "<pre>{$target_path} succesfully uploaded!</pre>" ; } } ?>
关键函数: 1 basename(path,suffix):函数返回路径中的文件名部分,如果可选参数suffix为空,则返回的文件名包含后缀名,反之不包含后缀名。
可以看到,服务器对上传文件的类型、内容没有做任何的检查、过滤,存在明显的文件上传漏洞,生成上传路径后,服务器会检查是否上传成功并返回相应提示信息。
Medium: 源代码:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 <?php if ( isset ( $_POST[ 'Upload' ] ) ) { $target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/" ; $target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] ); $uploaded_name = $_FILES[ 'uploaded' ][ 'name' ]; $uploaded_type = $_FILES[ 'uploaded' ][ 'type' ]; $uploaded_size = $_FILES[ 'uploaded' ][ 'size' ]; if ( ( $uploaded_type == "image/jpeg" || $uploaded_type == "image/png" ) && ( $uploaded_size < 100000 ) ) { if ( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) { echo '<pre>Your image was not uploaded.</pre>' ; } else { echo "<pre>{$target_path} succesfully uploaded!</pre>" ; } } else { echo '<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>' ; } } ?>
可以看到,服务器对上传文件的大小和类型做了限制。只允许上传小于 100000 字节并且文件type类型是image/jpeg或 image/png 的
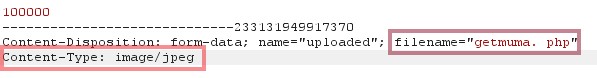
方法一:抓包修改文件的type 因为这里过滤的是文件的上传类型,而不是文件的后缀名
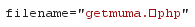
方法二:00截断 在php版本小于5.3.4的服务器中,当Magic_quote_gpc选项为off时,可以在文件名中使用%00截断
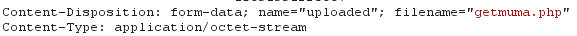
先上传一个木马,抓包:
修改后发送:
getmuma. php中的空格的16进制为20,需把他改为00
High: 源代码:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 <?php if ( isset ( $_POST[ 'Upload' ] ) ) { $target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/" ; $target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] ); $uploaded_name = $_FILES[ 'uploaded' ][ 'name' ]; $uploaded_ext = substr( $uploaded_name, strrpos( $uploaded_name, '.' ) + 1 ); $uploaded_size = $_FILES[ 'uploaded' ][ 'size' ]; $uploaded_tmp = $_FILES[ 'uploaded' ][ 'tmp_name' ]; if ( ( strtolower( $uploaded_ext ) == "jpg" || strtolower( $uploaded_ext ) == "jpeg" || strtolower( $uploaded_ext ) == "png" ) && ( $uploaded_size < 100000 ) && getimagesize( $uploaded_tmp ) ) { if ( !move_uploaded_file( $uploaded_tmp, $target_path ) ) { echo '<pre>Your image was not uploaded.</pre>' ; } else { echo "<pre>{$target_path} succesfully uploaded!</pre>" ; } } else { echo '<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>' ; } } ?>
关键函数: 1 2 3 4 5 strtolower() : 函数把字符串转换为小写。 strrpos(string,find,start):函数返回字符串find在另一字符串string中最后一次出现的位置,如果没有找到字符串则返回false ,可选参数start规定在何处开始搜索。 getimagesize(string filename) :函数会通过读取文件头,返回图片的长、宽等信息,如果没有相关的图片文件头,函数会报错。
High级别的代码读取文件名中最后一个”.”后的字符串,期望通过文件名来限制文件类型,因此要求上传文件名形式必须是”.jpg”、”.jpeg”、”.png”之一。同时,getimagesize函数更是限制了上传文件的文件头必须为图像类型
因为上传的文件为图片类型,因此服务器将上传的文件解析成图片文件,所以若向其发送请求时,服务器只会返回这个“图片”文件,并不会执行相应命令。这里可以借助Medium级别的文件包含漏洞来获取webshell权限,具体文件包含的方法可参考(Upload-labs)https://ddstick.github.io/2019/07/31/Upload-labs/#Pass-13-%E5%9B%BE%E7%89%87%E9%A9%AC
方法二:
Impossible 源代码:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 <?php if ( isset ( $_POST[ 'Upload' ] ) ) { checkToken( $_REQUEST[ 'user_token' ], $_SESSION[ 'session_token' ], 'index.php' ); $uploaded_name = $_FILES[ 'uploaded' ][ 'name' ]; $uploaded_ext = substr( $uploaded_name, strrpos( $uploaded_name, '.' ) + 1 ); $uploaded_size = $_FILES[ 'uploaded' ][ 'size' ]; $uploaded_type = $_FILES[ 'uploaded' ][ 'type' ]; $uploaded_tmp = $_FILES[ 'uploaded' ][ 'tmp_name' ]; $target_path = DVWA_WEB_PAGE_TO_ROOT . 'hackable/uploads/' ; $target_file = md5( uniqid() . $uploaded_name ) . '.' . $uploaded_ext; $temp_file = ( ( ini_get( 'upload_tmp_dir' ) == '' ) ? ( sys_get_temp_dir() ) : ( ini_get( 'upload_tmp_dir' ) ) ); $temp_file .= DIRECTORY_SEPARATOR . md5( uniqid() . $uploaded_name ) . '.' . $uploaded_ext; if ( ( strtolower( $uploaded_ext ) == 'jpg' || strtolower( $uploaded_ext ) == 'jpeg' || strtolower( $uploaded_ext ) == 'png' ) && ( $uploaded_size < 100000 ) && ( $uploaded_type == 'image/jpeg' || $uploaded_type == 'image/png' ) && getimagesize( $uploaded_tmp ) ) { if ( $uploaded_type == 'image/jpeg' ) { $img = imagecreatefromjpeg( $uploaded_tmp ); imagejpeg( $img, $temp_file, 100 ); } else { $img = imagecreatefrompng( $uploaded_tmp ); imagepng( $img, $temp_file, 9 ); } imagedestroy( $img ); if ( rename( $temp_file, ( getcwd() . DIRECTORY_SEPARATOR . $target_path . $target_file ) ) ) { echo "<pre><a href='${target_path}${target_file}'>${target_file}</a> succesfully uploaded!</pre>" ; } else { echo '<pre>Your image was not uploaded.</pre>' ; } if ( file_exists( $temp_file ) ) unlink( $temp_file ); } else { echo '<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>' ; } } generateSessionToken(); ?>
关键函数: 1 2 3 4 5 6 7 8 9 in_get(varname):函数返回相应选项的值 imagecreatefromjpeg ( filename ) :函数返回图片文件的图像标识,失败返回false imagejpeg ( image , filename , quality) :从image图像以filename为文件名创建一个JPEG图像,可选参数quality,范围从 0(最差质量,文件更小)到 100(最佳质量,文件最大)。 imagedestroy( img ) : 函数销毁图像资源 getchwd() 函数返回当前工作目录
可以看到,Impossible级别的代码对上传文件进行了重命名(为md5值,导致%00截断无法绕过过滤规则),加入Anti-CSRF token防护CSRF攻击,同时对文件的内容作了严格的检查,导致攻击者无法上传含有恶意脚本的文件
web安全之token和CSRF攻击https://blog.csdn.net/qq_15096707/article/details/51307024